Firewall as a Service

Protect your operations from cyber threats by fulfilling your security policy and rule management requirements with a cloud-managed firewall service. Safeguard your business against potential security breaches.
Contact us now!Cutting-edge Managed Firewall Service designed for cloud infrastructures, equipped to meet the security needs of modern digital environments
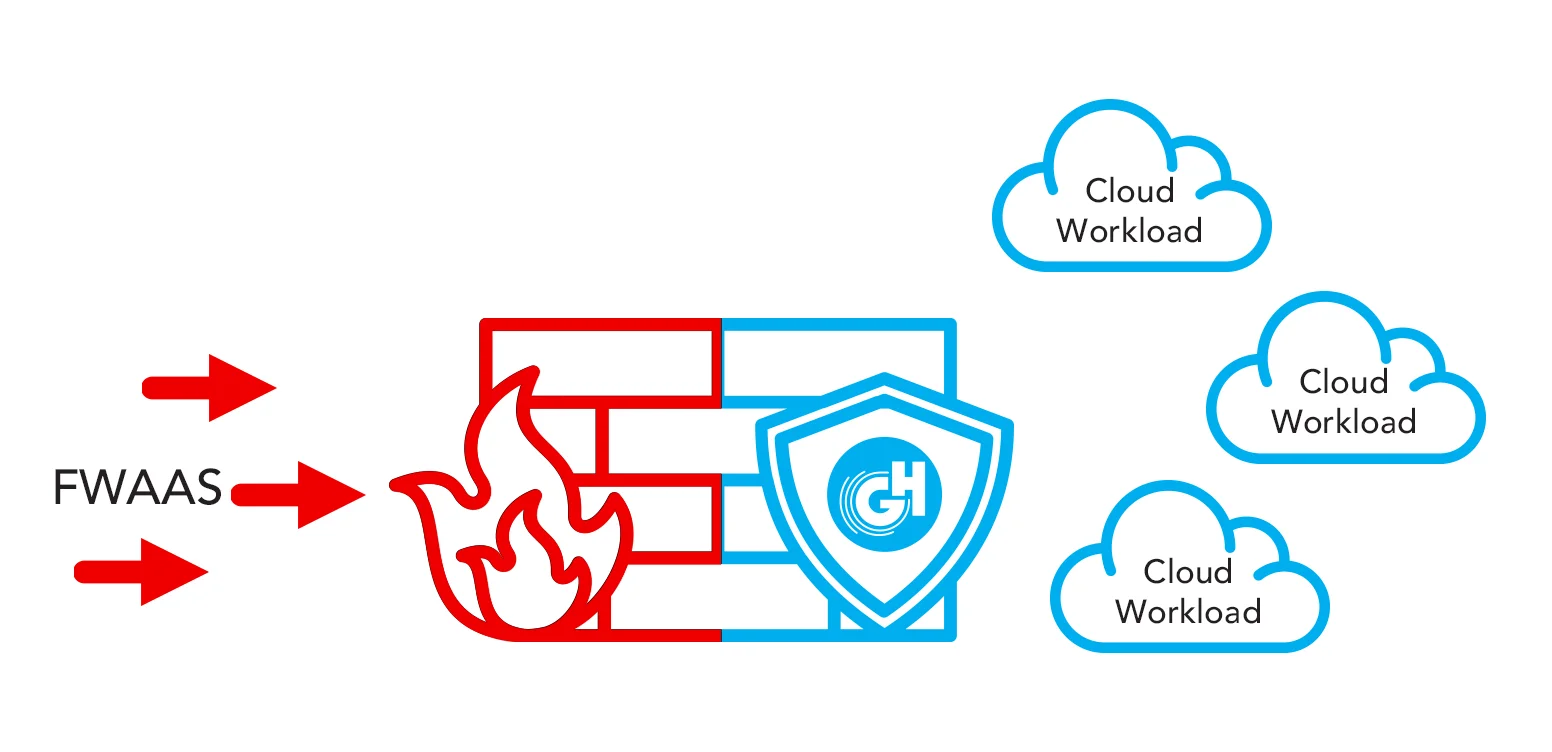
GlassHouse Firewall as a Service (FWaaS) (Managed Firewall Service) is a security service designed for cloud infrastructures. This Managed Firewall Service offers Layer 7 protection and Next Generation Firewall (NGFW) capabilities, available in both physical and software-based options.
Operated and managed continuously by GlassHouse's expert technical consultants 24/7, FWaaS comes with a monthly pricing model. It includes additional benefits such as application awareness and control, intrusion prevention, URL filtering, DNS security, and cloud-based threat intelligence to effectively filter harmful network traffic that may pose a risk to your organization.
GlassHouse FWaaS enhances security by reducing the attack surface through IPSec and SSL encryption protocols, ensuring secure connectivity and robust protection between endpoints and network resources. Advanced security features like two-factor authentication for mobile and desktop devices (iOS, Android, PC, Mac) are also supported.
As IT infrastructures become more complex and distributed, with remote work, mobile technologies, and container infrastructures on the rise, the need for proactive security measures is paramount. GlassHouse FWaaS addresses the evolving security landscape by providing comprehensive policy and rule management at the firewall layer, catering to the dynamic nature of modern endpoints and environments. Trust GlassHouse FWaaS to meet all your security needs in this critical area.
Complete the form to get in touch with us! Let's build the infrastructure of success for your IT operations together.
Discover the features of our Firewall as a Service.
Unveil the the advantages of GlassHouse Firewall as a Service

GlassHouse Cloud services reduce the operational intensity of the IT team. It helps your IT team to support the core business of the company instead of focusing on routine tasks related to maintaining infrastructure.Furthermore, it enables you to allocate your CAPEX budget towards investing in your core business activities instead of acquiring infrastructure components.
Streamline your operations with GlassHouse Firewall as a Service, offering a cost-effective, scalable, and efficient solution for advanced network security. Seamlessly integrated with all GlassHouse Cloud services, it provides quick and easy implementation.
Experience agility in your infrastructure by migrating to GlassHouse's cloud platform. Say goodbye to the delays of waiting for new hardware installations, as our firewall park is readily available for all clients around the clock. Once you transition your workloads to our platform, you can sidestep the hassle of managing software and hardware updates, maintenance, and repairs.
Customer Experiences
Blog content that may be of interest to you
Frequently Asked Questions
The customer can extend their on-premises firewall to our data center. This makes it possible to establish a hybrid architecture.