Disaster Recovery as a Service

Restore your data and applications seamlessly without loss using geographically redundant infrastructure for disasters!
Contact us now!Revert to any point in time with GlassHouse Disaster Recovery as a Service!
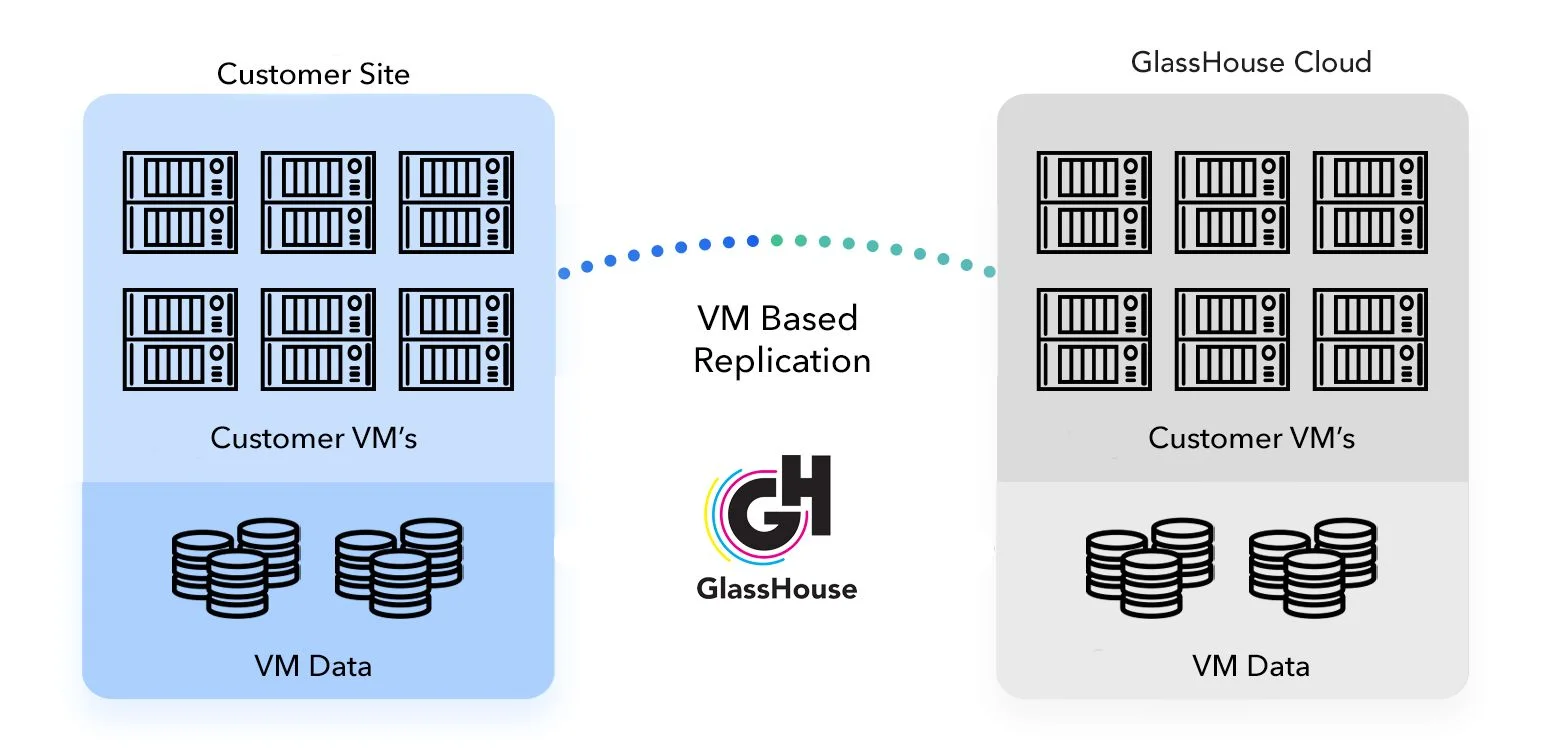
GlassHouse Disaster Recovery as a Service (DRaaS) is a cloud service that ensures business continuity against unexpected disasters. This service allows your operations to continue uninterrupted even during system failures. Typically accompanied by documentation for a Disaster Recovery Plan and a Business Continuity Plan, DRaaS leverages cloud capacity as a secondary infrastructure, replicating and backing up primary data and applications from the main data center. In the event of a disaster, the cloud environment transitions to the primary environment, enabling users to carry on with daily business activities. This setup allows your business to operate seamlessly during a disaster while primary systems undergo repairs.
DRaaS often serves as the initial cloud computing solution for IT organizations accustomed to on premises solutions. This service offers a low-risk operation by replicating data in the cloud while continuing to utilize on premises systems, enabling system testing post-initial backup. With years of experience, GlassHouse ensures your entire IT workload is protected and allows you to work safely in the GlassHouse Cloud data center in the event of a disaster.
Complete the form to get in touch with us! Let's build the infrastructure of success for your IT operations together.
Discover the features of our Disaster Recovery as a Service.
Unveil the benefits of GlassHouse Disaster Recovery as a Service!

GlassHouse DRaaS is hosted in Tier 4 data centers in Turkey, ensuring data security and compliance with local regulations. Compliant with Law No. 6698 on the Protection of Personal Data (KVKK), your data is stored securely, simplifying legal compliance and alleviating data security concerns. Full compliance with legal regulations applicable to financial and public sector organizations is also guaranteed.
Ease the burden on your IT teams and focus on your core business with GlassHouse DRaaS. Instead of dealing with infrastructure management and maintenance, you can direct your IT resources toward strategic projects. This helps your business innovate faster and gain a competitive advantage. Instead of purchasing IT infrastructure, you can use your CAPEX budget to invest in the growth and development of your business.
Customer Experiences
Blog content that may be of interest to you
Frequently Asked Questions
Data backup is a fundamental data protection strategy that involves creating copies of your corporate data and storing them securely for long-term retention, enabling point-in-time recovery (restore) in the event of data loss, corruption, or accidental deletion.
Disaster Recovery as a Service (DRaaS), however, goes beyond protecting data alone. It ensures business continuity by enabling your entire IT infrastructure and critical workloads to become operational in an alternate location within seconds in the event of a disaster.
Traditional backup processes are typically focused on achieving specific Recovery Point Objectives (RPO)—how much data loss is acceptable—whereas managed disaster recovery (Managed DR) solutions prioritize minimizing Recovery Time Objectives (RTO) by bringing systems back online almost instantly through failover capabilities.
GlassHouse DRaaS solutions leverage advanced replication technologies to reduce operational downtime to near zero in scenarios such as ransomware attacks or regional outages.
In short, backup serves as a secure archive of your data, while disaster recovery acts as a strategic business continuity platform that enables your organization to continue operating even during crises.